Background
Recently, I was working with a small marketing agency, and they asked if I could assist them with implementing windows security baselines in an effort to gain CIS and ISO 2700 compliance. I’d never heard of these controls. Read about CIS controls here. They provide industry-tested security settings. These settings can be deployed via GPO or MDM for all major Microsoft OS’s, O365, and Azure environments.
Purpose
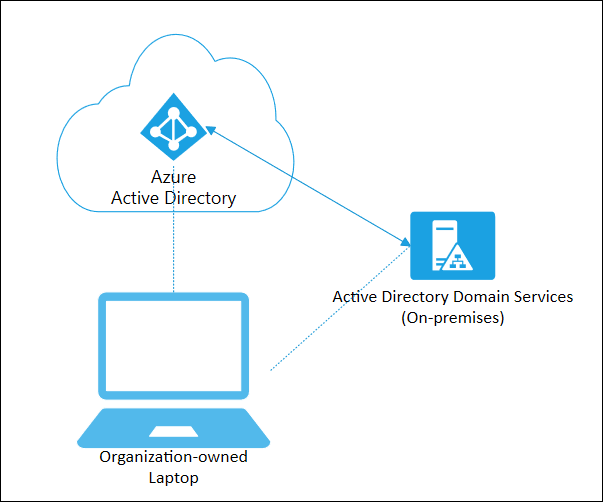
The below guide explains how to deploy the CIS benchmarks via group policy for an on-premise AD domain. It also explains how to validate your deployment using Policy Analyzer. Additionally, it provides some tips if you’ve never done this type of work and want to introduce some level of CIS compliance into your environment.
1/ Getting started
Define the scope for your deployment. Below are some questions myself and the client discussed to understand what we needed to do (example answers in green). It’s important to know these boundaries, so don’t accidentally deploy controls that aren’t required. Your audit report may guide you here, but remember – any introduction of new security settings is likely to cause some disruption at some point in time, so you should have a good awareness of where you are introducing the change and what services may be affected.
- What OS’s are in circulation within the environment? Windows Server 2019 (2x Domain controllers and 12 member servers) Windows 10 1901 (5 client devices). It’s important to know whether you’re working on Domain Member or Domain Controller because server-specific CIS controls are separated by server role.
- Do we want to deploy CIS controls to harden servers, desktops, domain controllers or all endpoints? We want to harden the DC’s and Servers only, no client devices.
- Can we feasibly introduce the new security controls without any risk to production operations? Yes, create a new group policy OU structure with a test OU and a test virtual server.
- If there is risk, how can we mitigate it and what is the rollback plan? Remove the GPO links and rebuild the test virtual server. In production, we’ll need to identify the problematic setting and remediate via group policy or local registry if necessary.
2/ Download the Microsoft SCT and CIS benchmarks
SCT contains the CIS benchmarks for all supported OS’s as well as several tools for helping you implement them. The only tool I had use for was Policy Analyzer.
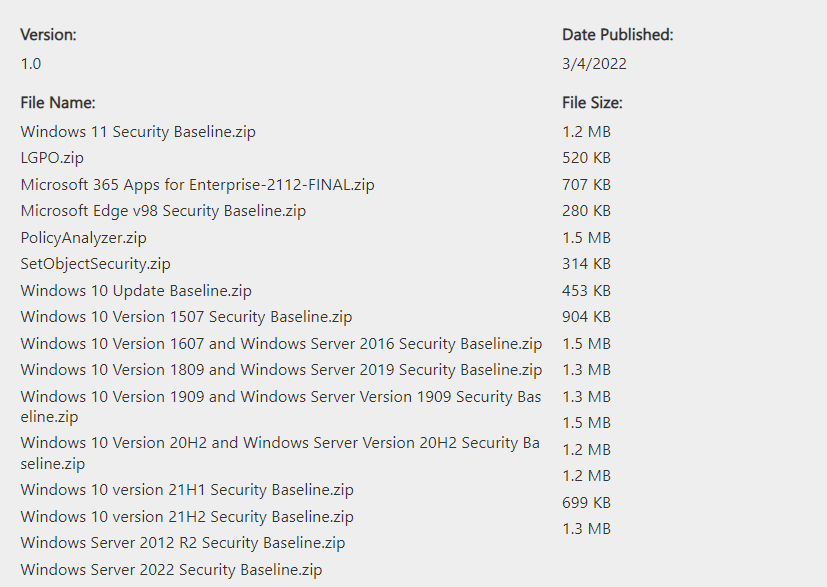
The OS’s are paired Client + Server by their release cadence so you’ll notice Windows 10 1809 and Server 2019 security baselines in a single .zip
Extracting the baselines for your environment you’ll see the following folder structure.

Documentation: Contains Excel reports covering release notes and change records for the controls.
GP Reports: *useful* HTML reports of the CIS security controls.
GPO’s: the CIS controls as GPO’s, ready for importing into GPMC.
Local_Script: Powershell scripts that apply the CIS controls to the local policy of a machine, useful if you want to test the settings in isolation (and not use group policy).
Templates: ADML and ADMX files used by the CIS GPO’s.
3/ Using Policy Analyzer to review conflicts
At this point you’re ready to compare the incoming CIS controls against your existing GPOs and check for any conflicts. You’ll need to use Policy Analyzer.exe to perform the comparison and I recommend you take a backup of existing, actively used GPOs before getting started.
- Take a backup of your existing Group Policy objects that are actively in use: it’s necessary to do this for 2 reasons; firstly, when you generate a comparison report in Policy Analyzer it’s much, much easier to identify where a conflict exists and remediate it when you have your existing GPOs individually compared instead of using ‘effective state’ (more on this in next step), secondly, you might screw up! So it’s always worth having a backup 🙂
Once backed up, let’s import the CIS GPOs into Policy Analyzer, launch the tool and click Add > File > Add files from GPO(s)…
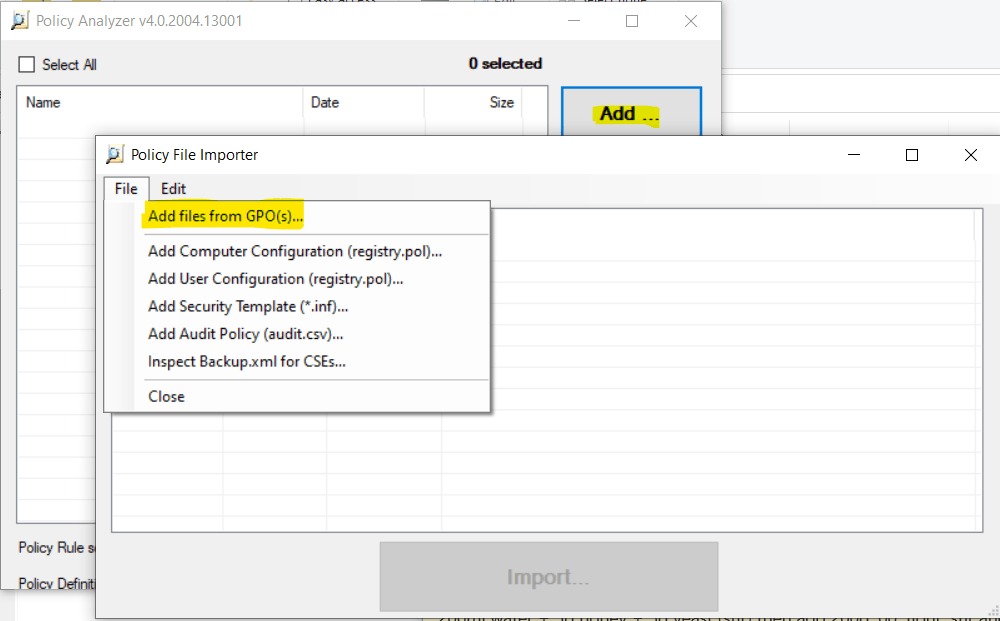
Select the folder containing the CIS controls
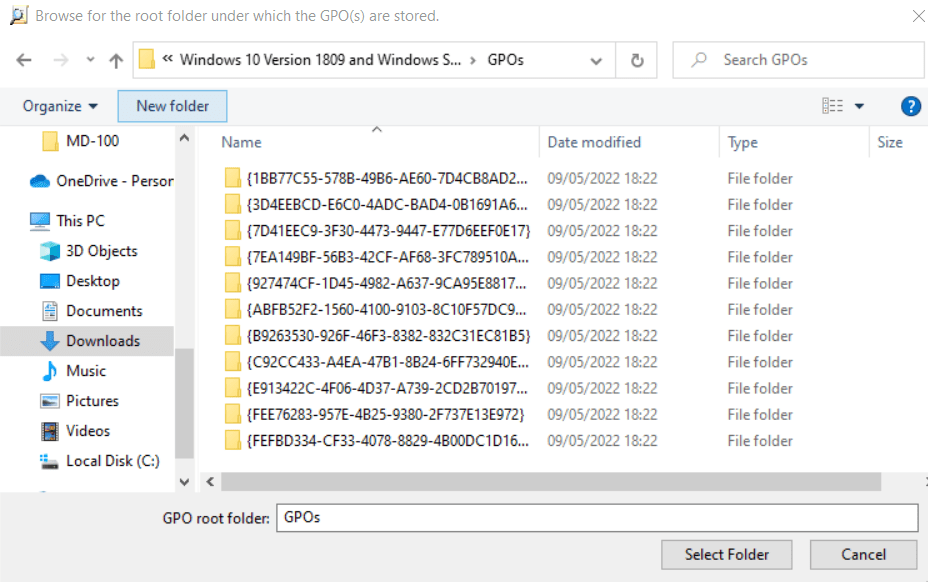
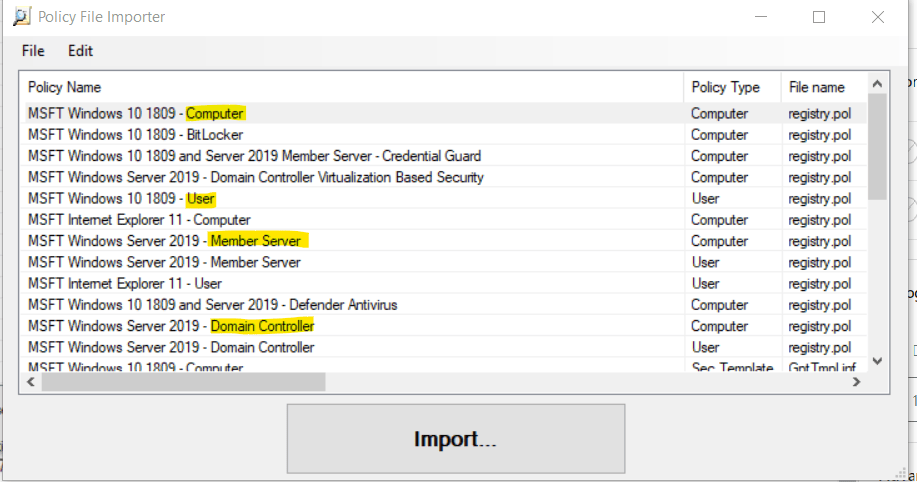
Now select the relevant GPOs for your environment, our earlier scoping exercise should help here and as you’ll see below some policies are for member servers, domain controllers, user settings or computer settings – so be aware of the differences in the targeted objects or role of a given GPO.
You’ll be prompted to save a .PolicyRules file – this is just a reference file for PA.
Once complete, you’ll see an entry for your newly imported GPOs and you now have the option to compare the controls to the local machines ‘Effective state’. In the results you’ll see two columns, your baseline (the CIS GPO) and the Effective State (your local machines state with group policy applied). Conflicts are highlighted, Grey is no existing setting is configured.
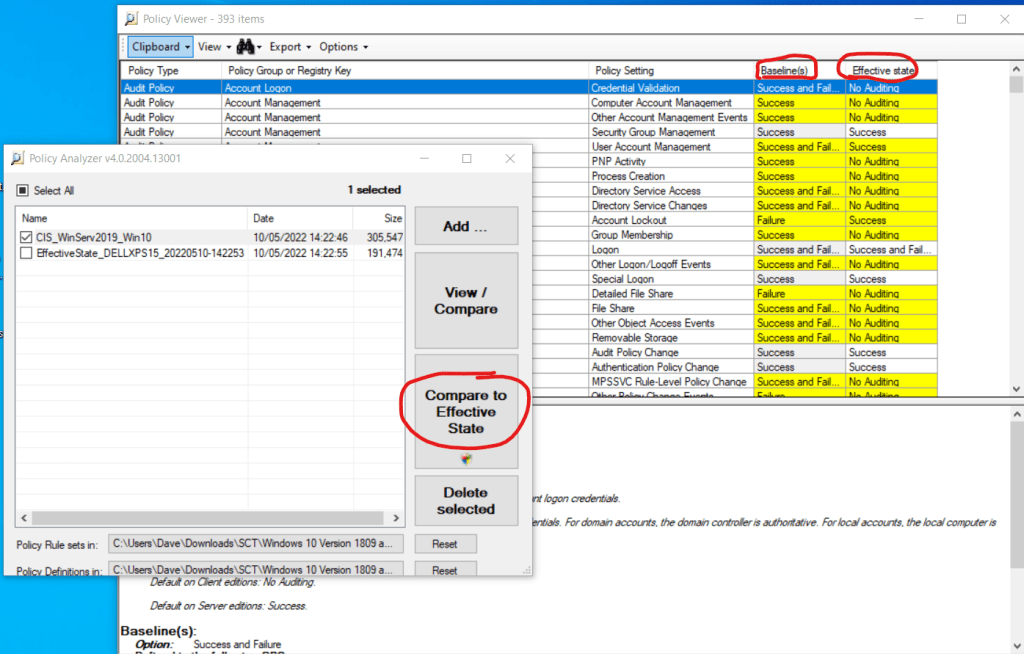
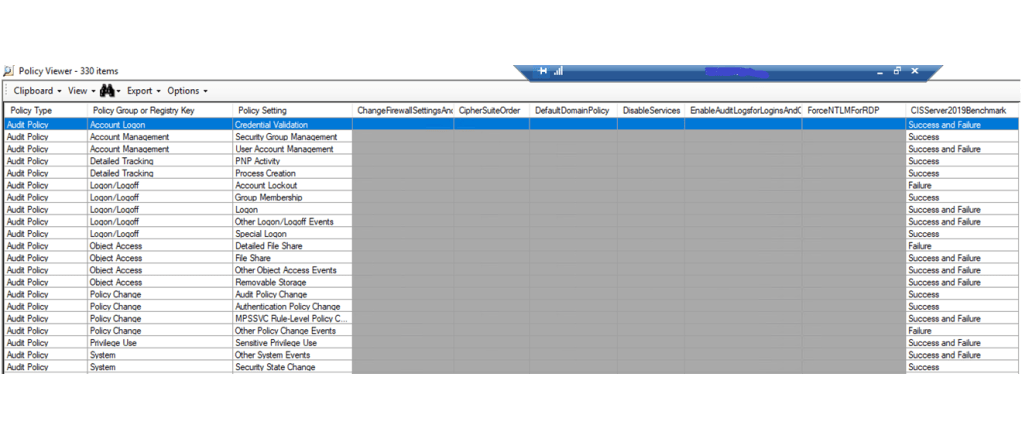
The default view is useful but it doesn’t show you which of your existing GPOs are conflicting with the CIS controls. To see this, we’ll need to import the GPOs you backed up earlier into Policy Analyzer. To do this, repeat the steps you’ve just taken to import the CIS GPOs, but point to your backed up GPO files and then save the .policyrules file. Re-run the comparison but this time don’t compare to the Effective State, instead select the CIS controls and your existing GPOs and click View/Compare.
The view will now contain a column per-GPO, making it much easier for you to identify which policy contains the conflicting setting and adjust accordingly.
Import CIS GPOs and ADMX/L templates into GPMC
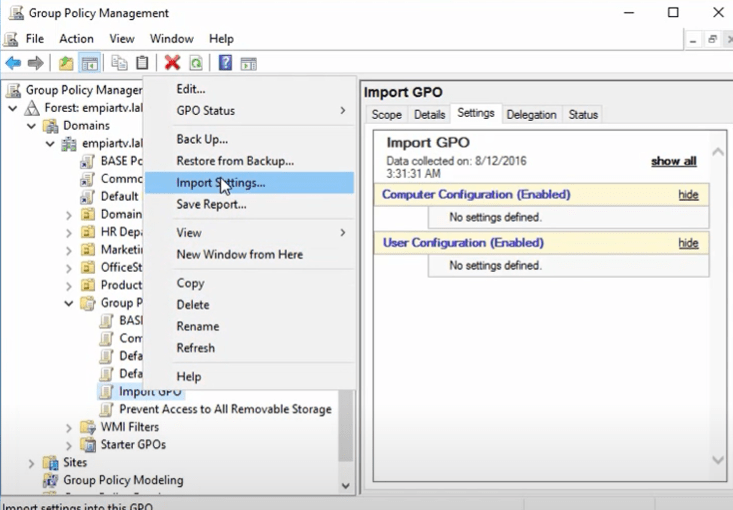
At this point you’ve got the nuts and bolts to perform comparisons and find conflicts. I would recommend you do a Export > All results to Excel to keep a record of your domain state before you start meddling with group policy. Spend time reviewing the conflicts and reading through the new incoming settings, when you’ve resolved the conflicts (either by editing your existing GPOs, or muting the settings in the CIS GPOs) you now need to import the CIS GPO files into GPMC. Here is a useful guide for doing this alternatively, or (slower) you can manually create a new Group Policy Object > Right click > Import Settings and select the CIS GPOs one by one.
Remember to also import the ADMX and ADML templates from the Templates folder into your central group policy store.
Conclusion
To recap, we identified the scope of devices you want to harden and what OS mix operates within your domain. We then extracted the baselines and compared them to the existing state of an endpoint and/or all existing GPOs to remediate conflicts, you’ve imported all the security policies into your GPMC console and are now ready to deploy the controls within your domain.
At this point I would recommend you have some test machines to deploy the new GPOs to and monitor the progress. I hope this post has been of some use to you and good luck. If you’d like to make a donation you can do so below.
https://www.buymeacoffee.com/desktopsurgery
Cheers,
Dave